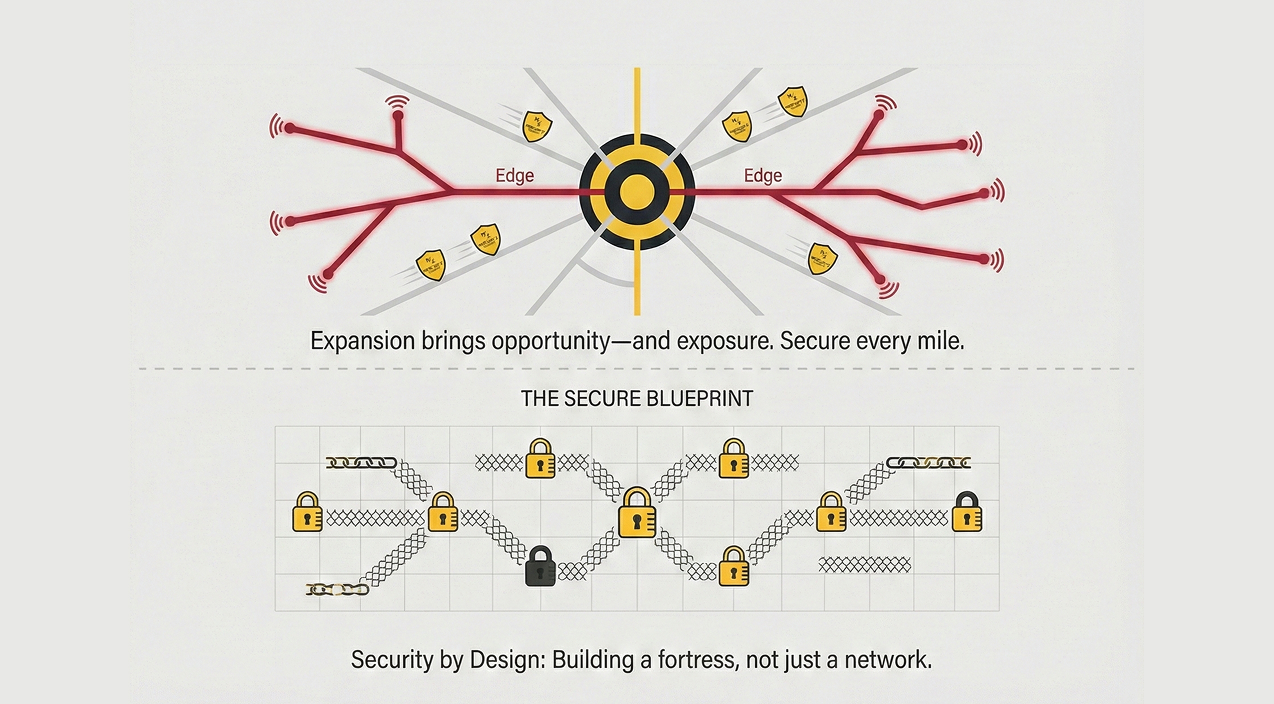
BEAD cybersecurity compliance is now a top priority for every mile of fiber laid. Every new subscriber connected is a win for digital equity. However, in the eyes of a cybercriminal, that new infrastructure represents a fresh attack surface.
As regional ISPs and cooperatives rapidly expand into unserved territories, they are no longer “too small to be noticed.” In 2026, rural networks have become prime targets for ransomware groups. These hackers bet on the fact that smaller providers may lack the sophisticated defenses of national carriers. Furthermore, the NTIA’s official BEAD guidance emphasizes that security is a pillar of the program. When you’ve just spent millions on a build-out, you cannot afford a network-wide freeze. Such an event erodes customer trust on Day 1.
The Mandatory Mandate for BEAD Cybersecurity Compliance
For recipients of federal funding, security isn’t just a best practice. Instead, it is a contractual obligation. The National Telecommunications and Information Administration (NTIA) has made its stance clear. Subgrantees must have a robust risk management plan. This plan must align strictly with the NIST Cybersecurity Framework.
The industry shift in 2026 favors “Security by Design.” This means engineers do not “bolt on” security after the network is live. Instead, they weave protection into the OSP/ISP engineering phase.
Why Resilience Matters
The financial stakes are higher than ever. Consider these critical statistics:
- The Financial Toll: The average cost of a ransomware attack in the telecom sector now exceeds $1.5 million in recovery costs. This figure excludes the actual ransom payment.
- The Skills Gap: Recent data from the World Economic Forum shows that 63% of organizations fall victim to attacks because they lack in-house security skills.
- Expert Insight: “In the broadband race, speed is important, but resilience is everything,” says the Mercury Z Security Lead. “A network without BEAD cybersecurity compliance is just a high-speed delivery system for a data breach.”
Mercury Z: Your Shield for New Deployments
As you finalize your BEAD-funded builds, you need an experienced partner. You need someone who understands the physical layer and the digital layer. Mercury Z provides the end-to-end protection required to satisfy federal auditors.
- NIST-Aligned Penetration Testing: We identify “open windows” in your new infrastructure before a hacker does. Our team provides deep, manual analysis of your network’s vulnerabilities.
- Vulnerability Assessments: We offer continuous monitoring. This ensures your security posture stays strong as your network grows.
- Engineering-Integrated Security: We handle OSP/ISP Engineering and CAD drafting. Therefore, we design your network with security in mind from the start. We ensure that physical access points remain protected and logical segmentations stay enforced.
How Mercury Z Can Help
Is your plan ready for a federal audit? Mercury Z offers a comprehensive BEAD cybersecurity compliance audit. We will review your current risk management plan against NIST standards. Additionally, we will perform a vulnerability scan to ensure your new “Edge” is actually a “Shield.”
Is Your Network Ready for BEAD Cybersecurity Compliance?
Are you prepared to meet the strict NIST standards required for your federal funding, or is your new infrastructure leaving you exposed? Don’t let a compliance gap or a preventable ransomware attack derail your expansion. At Mercury Z, we’ve got you covered with the expert engineering and security audits you need to stay protected and audit-ready from Day 1.

